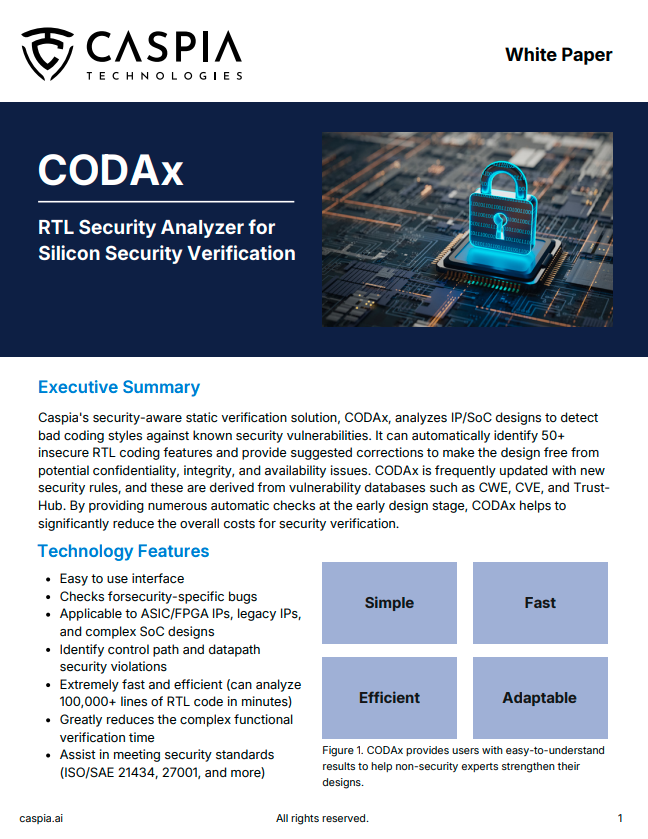
CODAx
Simple and Fully Automated Static Auditing Solution for SoC Security Verification
About CODAx
Caspia’s security-aware static verification solution, CODAx, analyzes semiconductor design code to detect bad coding styles against security weaknesses. It can automatically identify 150+ insecure RTL coding features that are tied to today’s public sources, such as CWEs, and Caspia’s unique research in the field. CODAx provide suggested corrections to make the design free from potential confidentiality, integrity, and availability issues.
- Fast security verification at RTL with easy-to-use interface for non-security engineers
- Easily expandable with new rules based on recent research and publicly disclosed vulnerabilities
- Applicable to ASIC/FPGA IPs, legacy IPs, and complex SoC designs
- Assist in meeting security standards (ISO 21434, DO-254, and more)
CODAx V2026.2 Latest Release - Out Now!
Key Features
CODAx is purpose-built to safeguard RTL designs against evolving hardware security threats. By rigorously examining code and design structures, it uncovers vulnerabilities that could compromise confidentiality, integrity, or reliability, giving engineers the visibility they need to strengthen critical systems.
Beyond detection, CODAx empowers designers with actionable insights, intuitive reporting, and practical fixes that streamline the resolution process. With seamless workflow integration and tailored evaluations, CODAx makes advanced hardware security accessible to teams of all expertise levels.
These include:

Datapath Analysis
CODAx rigorously analyzes the datapath – the core component for data transfer and processing – to detect vulnerabilities such as improper handling, corruption, or breaches, ensuring robust protection of system confidentiality, integrity, and availability.
Report Generation
CODAx generates clear, detailed reports that describe detected vulnerabilities, their potential impacts, and recommended revisions, empowering designers of all expertise levels to enhance RTL security and understanding of hardware security principles.
Controlpath Analysis
CODAx analyzes control paths in Finite State Machines (FSMs) to identify vulnerabilities from attack vectors like fault injection or DoS, while detecting unauthorized control signal modifications to safeguard hardware integrity and reliability.

Suggested Fixes
CODAx goes beyond detection by providing tailored fixes and detailed guidance for each identified vulnerability in the datapath or control-flow, giving designers actionable insights for fast and effective resolution.

Root-Cause Analysis
CODAx performs root-cause analysis to pinpoint the exact RTL code behind security violations, enabling designers to address both symptoms and underlying weaknesses to strengthen overall component security.

Licensing
CODAx is available for licensing with tailored evaluations to ensure seamless integration into RTL workflows and demonstrate how it enhances hardware security.
Security Flow
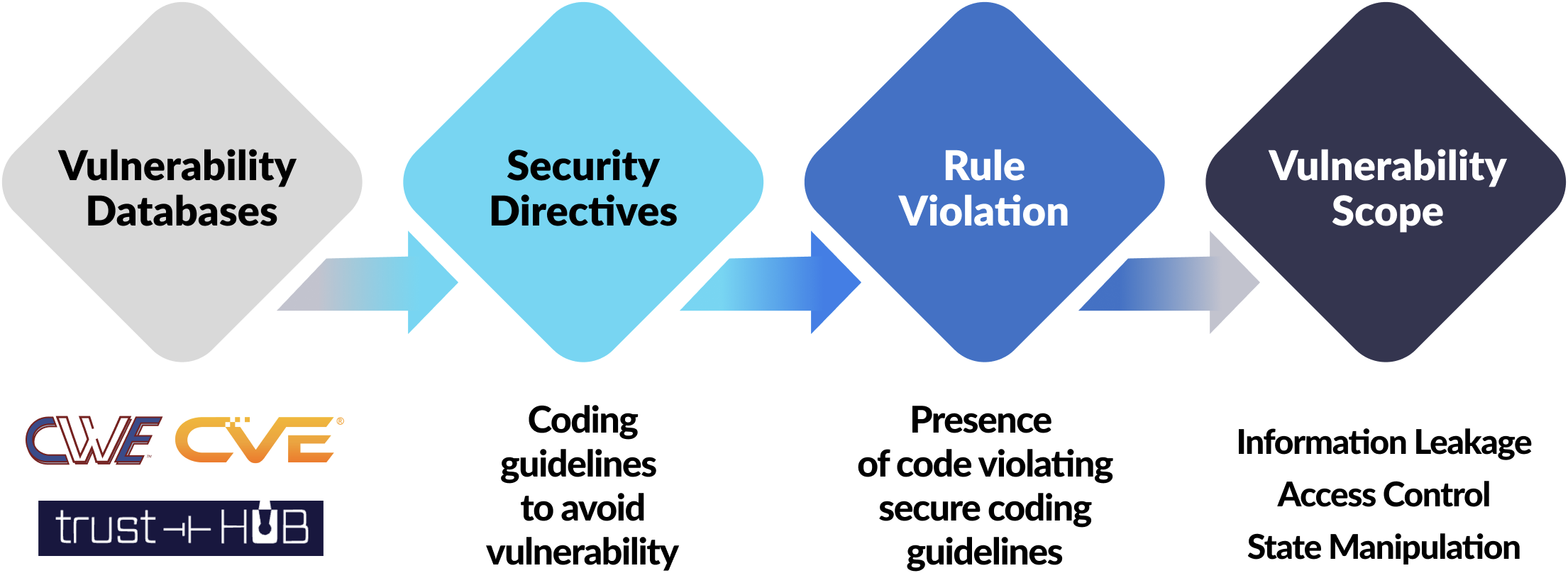
Detect early, reduce cost later.
CODAx database continues to be updated with new security directives & rules
- Make your designs safer
- Make your RTL design process security-aware
- Train designers about secure coding practices
- Compatibility with security protocols